Introduction to Cyber Security

Introduction to Cyber Security
- Cyber security is the task of shielding networks and computer systems from cyber theft or attack, related to hardware, software or electronic data.

What is meant by Malware?
Malware stands for Malicious Software, It is a program devised to invade and attack the systems outwardly the owner's permission, It is the broad term for comprising of all distinct sorts of warnings to your systems such as spyware, Trojans horses, viruses, worms, rootkits, adware, scare ware. On the contrary, software which causes accidental damage is called a bug.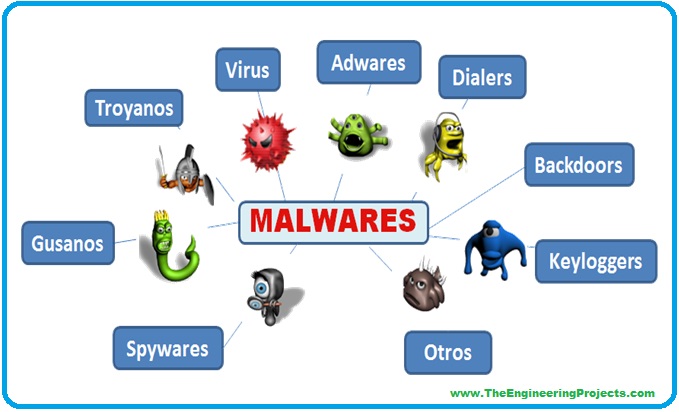
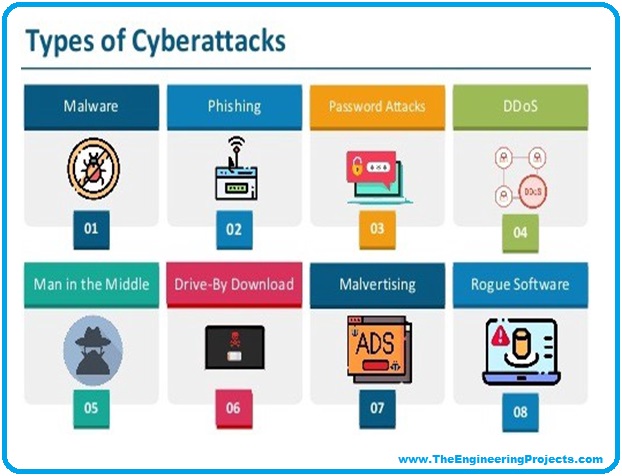
Types of Cyber Attacks
- As you can see in the image below, some enlisted malware existed since the beginning of internet.
- Let's have a look at them one by one:
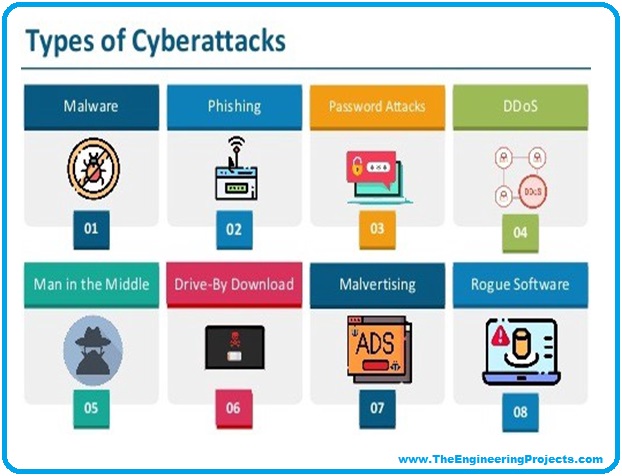
1. Phishing
They are the attack which is sent as a link to the user through the email posing a genuine party asking for the data. The users have to click on the link and enter the personal data. Over the years the phishing emails have become more sophisticated and often settle in the section of spam.2. Password attack
A password attack can be defined as the attacker requests for the password from the user and try to crack it to gather the sensitive data and access the computer system.3. DDoS
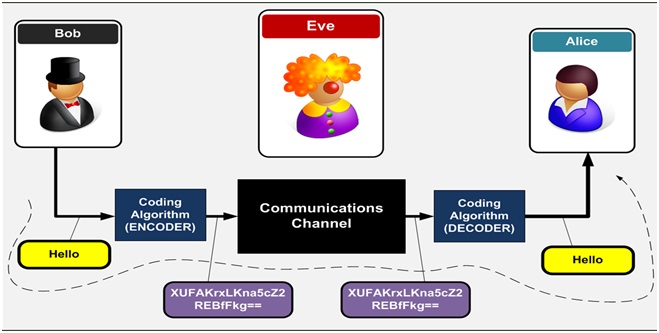
DDoS stands for Distributive Denial of Service, in this process, the attacker transmits a huge amount of data to the network that is making several connection requests unto the network gets trafficked and unable to function.4. Man In the middle
There are possibilities of this type of attack when user exchanges the data online, your smartphone is connected to the website the MITM attack can obtain the data from the end-users and the entity you are communicating with. For example, a middle man can communicate with you portraying your bank and contact the bank impersonating you. Then would receive the data from both the sides and transfer it to the third parties, which can include sensitive information such as your account number, your credit or debit card number or your IBAN5. Drive-by Downloads
A program is downloaded by the website by just visiting them through malware on that specific website. It doesn't ask for the permission of the user or to take any action.6. Malware Advertising (Malvertising)
A malicious code threatens your computer system downloaded when you click on the bogus add.7. Rogue software
Security software that keeps your system safe.History of cyber attacks
Not only we as individuals are vulnerable to the attacks but the organizations or companies aren't safe either. For instance a well-known graphic software company, Adobe Photoshop was hacked despite the high-security systems and they had to go through major cyber breaches where all the sensitive data and confidentiality was compromised, eBay, AOL, Ever note were also affected by the cyber breaches. So not only individuals but the bigger organization are spontaneously being attacked by the hackers.
Protection from Cyber attacks
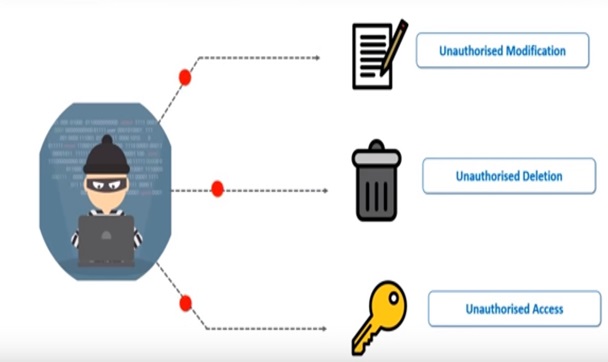
By reading about cyber breaches and threats to the security one must be questioning that is there any mechanisms or protocols that can provide full-proof security to the computer systems? And the answer is "Yes" and that is called cyber security. In the context of information technology, the physical and cyber security comprised of the security, the enterprises used them to protect them against the access of unauthorized companies or data centers. Information security is created to sustain the confidentiality and availability of data in a subset of cyber security. So cyber security can help counter the cyber breaches, identity theft, and aid and risk management. So when an organization has a strong function of network security and an efficient disturbance response plan then it is capable of defending and protecting the data against the attack.What are we exactly trying to protect?
We protect ourselves against three activities and they are,- Unauthorized Modification
- Unauthorized Access
- Unauthorized Deletion
CONFIDENTIALITY
confidentiality is commensurate to privacy actions engaged to assure confidentiality are created to counter sensitive information from reaching the spies while making certain that the right people can access it. Access must be restricted to those allowed to view the data in question is as regular as well for data to be classified according to the volume and type of destruction that could be done shouldn't slip into the unintended hands. More or less stringed measures can then be implemented to those categories. Sometimes safeguarding data confidentiality may include special training for those privies to such documents, such training would typically include security jeopardies that could threaten this information, training can benefit familiarize authorized people with risk factors and how to shield against them. Further phases of training can include password and password related best practices and information above human communications methods to prevent them from twisting data handling rules with good intentions and potentially unfavorable outcomes.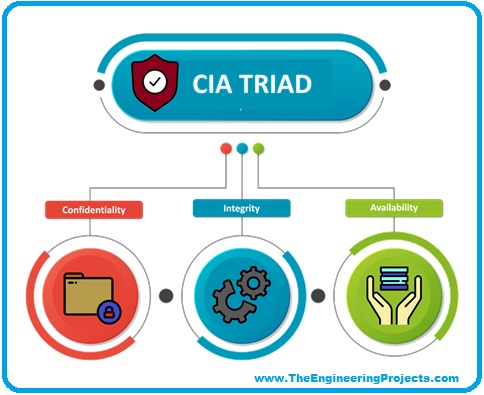
INTEGRITY
Integrity includes sustaining consistency, efficiency, and trustworthiness over its intact lifecycle. Data must not be changed or altered by third parties and authorized individuals and the actions must be used to ensure this. For example in a data infringement of confidentiality, these measures include file permissions and user access controls accounts. Accounts may be used to prevent false changes and accidental deletion by authorized users becoming an obstacle. Furthermore, some means must be in place to detect any fluctuations in data that might transpire as a result of non-human generated issues, such as, electromagnetic vibrations or silver crash. Some data might involve checksums, even cryptographic checksum for verification of the integrity backup or redundancies must be prepared to reestablish affected data to its correct state.AVAILABILITY
Availability is best guarded by austere maintaining of all hardware operating best instantly when required and maintaining an accurately functional operating system that is free of software frictions. It is also necessary to keep all the operating system upgrades producing enough transmission bandwidth and preventing the occurrence of bottlenecks are equally significant. Redundancy failover and even high availability clump can lessen severe consequences when hardware issues do occur fast. As an adaptive failure restoration is imperative for the worst-case scenario that the capacity is reliant on the existence of a comprehensive disaster recovery plan shields against data loss or interference in the connection must include. Unpredictable events such as natural disasters and files to prevent data loss from such incidents, a backup copy must be stored in a geographically secluded area, perhaps in a fire-resistant liquid safe place. Extra security equipment or software such as firewalls and proxy servers can secure us against downtimes and unreachable data due to malicious actions, such as a denial of service attacks and network intrusions. So now that we have seen what we are trying to protect, implement when trying to protect ourselves on the other hand, we should also know the ways that we protect ourselves when we are attacked by cyber systems. So the first action that we mitigate any type of intervention is to detect the malware or the cyber threat that is being currently going on in your organization. Next, we have to analyze and evaluate all the affected parties and the file systems that have been compromised and, in the end, we have to repair the whole procedure so that our organization can come back to its whole streaming state without any cyber breaches. So how it is exactly done? This can be done by considering three factors. Vulnerability, Threat and, Risk. So let me explain all of them precisely.Vulnerability
It can be defined as a known weakness of an asset that can be misused by one or more attackers, in other words, a hidden issue that enables an intervention to be successful. For example, when an employee or a member of an organization is fired and you forget to disable the access of external accounts, change logins and remove their names from the company credit cards, this will jeopardies your business willingly or unwillingly. However, most of the vulnerabilities are exploited by the authorized attackers on a human typing on the other side of the system.
THREAT
A threat can be described as a newly created disturbance with the potential to harm a system or your whole company. There are three types of threats.- National Threats like Earthquakes tornados, hurricanes, tsunami and floods.
- Unintentional Threat i.e. an employee mistakenly obtaining the sensitive data.
- Intentional Threats, there are many examples of intentional threats such as Malware, adware, spyware companies are the actions of disgruntled employees. To add up, worm and viruses are characterized as threats because they could potentially cause harm to your organization through exposure to a programmed intervention as opposed to executed by human beings. Although these threats are commonly outside of one's control and difficult to predict before it happens. It is requisite to take legit measures to assess intimidations systematically.
RISK
Risk refers to the potential to the loss and damage when a threat exploits a vulnerability. Examples including financial damage as a result of business agitation, loss of privacy, damage to reputation, legal associations and even the destruction of career or life. Risk can also be defined as the product of threat and vulnerability. You can reduce the potential for risk by engineering and executing a risk management plan, the following are the key aspects for developing your risk management strategy. First, we are required to evaluate risk and circumscribe needs, when engineering and implementing a risk assessment framework, it is crucial to prioritize the most related breaches that need to be discussed. All the frequency may differ in each organization. This level of assessment must be done regularly. Next, we also have to include a stakeholder perspective that includes the business owners as well as employees, consumers, and even merchants. All of these professionals have the potential to negatively impact the organization but they can be an asset in helping to mitigate risks at the same time. Since risk management is the key to cyber security.×
![]()