What is Edge Computing?

Hi Friends! Hope you’re well today. In this post, I’ll walk you through What is Edge Computing?
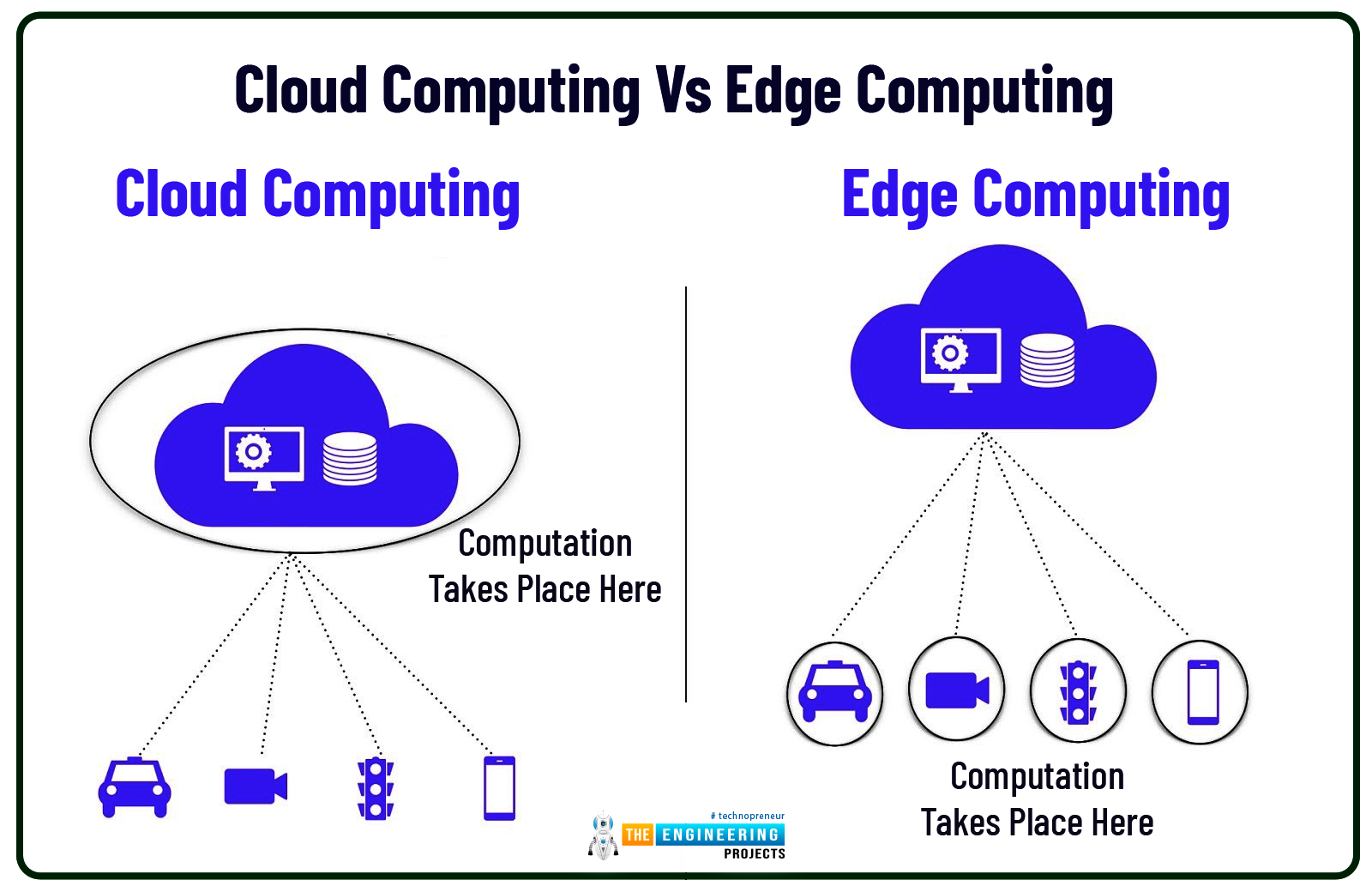
Edge computing is the extension of cloud computing. Cloud computing is used for data storage, data management, and data processing. While Edge Computing does serve the same purpose with one difference: edge processing is carried out near the edge of the network which means data is processed near the location where it’s produced instead of relying on the remote location of the cloud server.
Confused?
Don’t be.
We’ll touch on this further in this article.
Curious to know more about what is edge computing, the difference between edge computing and cloud computing, benefits, and applications?
Keep reading.
What is Edge Computing?
Edge computing is the process where data is processed near or at the point where it’s produced. The word computing here is used for the data being processed. Simply put, Edge computing allows the data to be processed closer to the source of data (like computers, cell phones) rather than relying on the cloud with data centers. This process is used to reduce bandwidth and latency issues.
For instance, Surveillance cameras. When these cameras are required simultaneously to record a video, if you use cloud computing and run the feed through the cloud, it will increase its latency (latency is the time delay between actual data and processed data) and reduce the quality of the video.
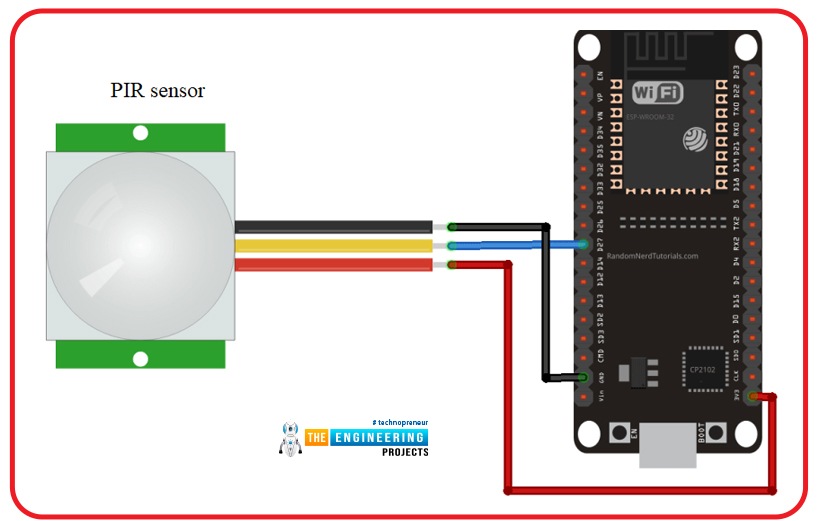
This is where edge computing comes in handy. In this particular case, we can install a motion detector sensor that will sense the movement of the physical beings around the camera. This motion-sensing device will act as an edge device that is installed near the data source (camera). When live feed data is processed near the edge devices instead of the cloud or data centers, it would increase the video quality and practically reduce the latency to zero.
Cloud storage takes more time to process and store data, while edge computing can locally process data in less time. The market of edge computing is expected to grow from $3.5 billion to $43.4 billion by 2027, according to experts in Grand View Research. Many mobile network carriers are willing to apply edge computing into their 5G deployment to improve their data processing speed instead of picking the cloud server.
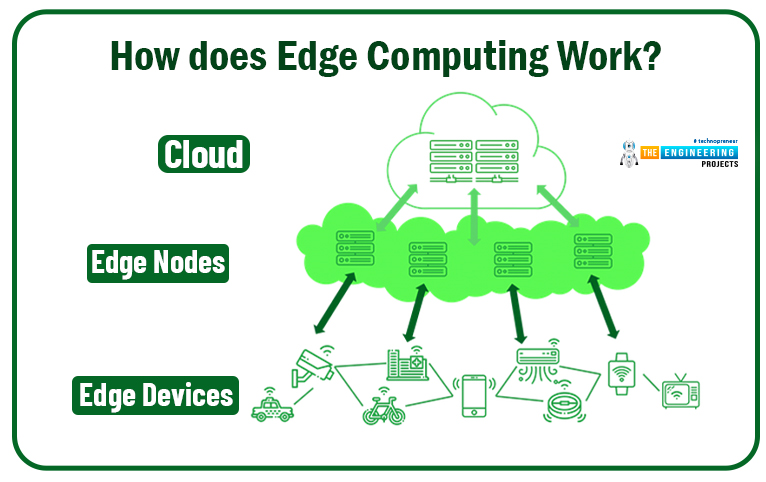
How does Edge Computing Work?
Normally in cloud computing, two components are used: the device and the cloud server. In edge computing an intermediate node is introduced between the device and the cloud server, this node is called an edge device.
How data was stored in data centers before edge computing stepped in? Yes, this is the main question to discuss before we explain how edge computing works.
Before edge computing, data was gathered from distributed locations. This data was then sent to the data center which could be an in-house facility or the public cloud. These data centers were used to process the stored data.
In edge computing that data processing is carried out near or at the point from where data originates. This is very useful for making real-time decisions that are time-sensitive. Like in the case of automatic cars interacting with each other.
Plus, less computing power is required in edge computing since we don’t need to push back all data to the data center. Like in the case of a motion-detecting sensor installed near the camera. In case we require a video of a particular instance, we need to pull out the entire information recorded inside the camera to reach that particular instant clip. However, when the motion sensor is installed near the camera that acts as an edge device, we only require that information where that sensor has detected the movement of any physical beings, and we can easily discard the rest of the information and we don’t need to store that information into the cloud server.
Know that edge data centers are not the only way to store and process data. Rather, edge computing involves the network of different technologies. Some IoT devices can become a part of this edge computing and can process data onboard and send that data to the smartphone or edge server to do the difficult calculations and efficiently handle the data processing.
Cloud Computing Vs Edge Computing
An edge computing environment is developed using a network of data centers spread across the globe. The data centers in edge computing are different than the data centers at cloud computing. In former data centers store and process information locally and comes with the ability to replicate and transfer that information to other locations. While in the latter, data centers are located hundreds of thousands of miles away. The network latency issues and unpredictable pricing model of the cloud storage allow the organizations to prefer private data centers and edge locations over public cloud.
Google Cloud, Amazon Web Services, and Microsoft Azure are the best examples of cloud computing. They use cloud computing infrastructure which is developed to transfer the data from data source to one centralized location called data centers.
While facial recognition lock feature of the iPhone uses an edge computing model. If the data in this feature runs through cloud computing, it would take too much time to process data, while the edge computing device, which is the iPhone itself, in this case, does this processing within a few seconds and unlocks the mobile screen.
For massive data storage or for software or apps that don’t require real-time processing needs, cloud computing is the better solution and is commonly called the centralized approach. And if you require less storage with more real-time processing power that is carried out locally, edge computing is the answer and is called a decentralized approach where not a single person is making a decision, rather decision power is distributed across multiple individuals or teams.
Know that companies typically harness the power of both cloud computing and edge computing to develop advanced IoT frameworks. These two infrastructures are not opposite but are complementary for designing a modern framework.
Difference between Edge Computing and IoT
Edge computing is a form of distributed computing infrastructure that is location-sensitive while IoT is a technology that can use edge computing to its advantage. Edge computing is a process that brings the processing data as near to an IoT device as possible.
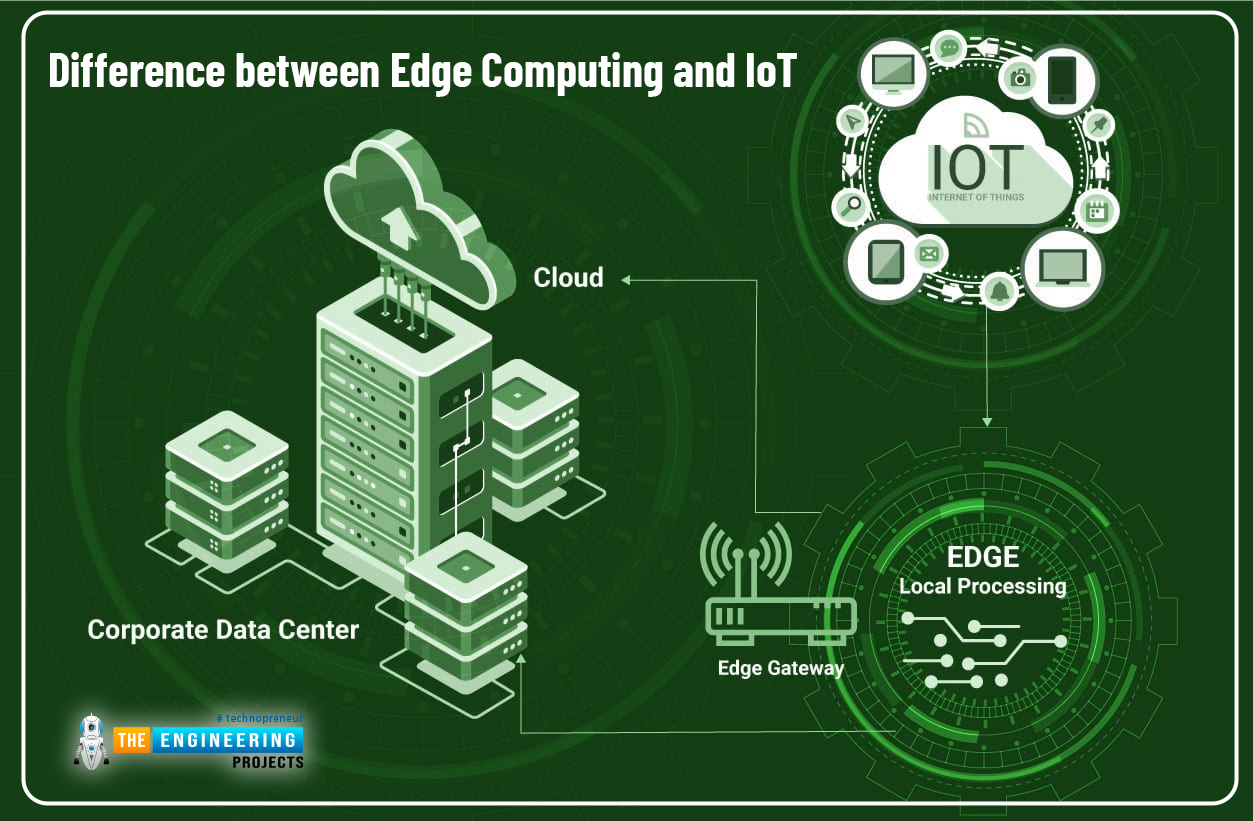
Don’t confuse an edge device with an IoT device. The device is the physical device where data is stored and processed while the IoT device, on the other hand, is the device connected to the internet. It is nothing but the source of the data.
Benefits of Edge Computing
Edge computing is changing the way how data is stored and processed. This gives a more consistent and reliable experience at a significantly lower cost.
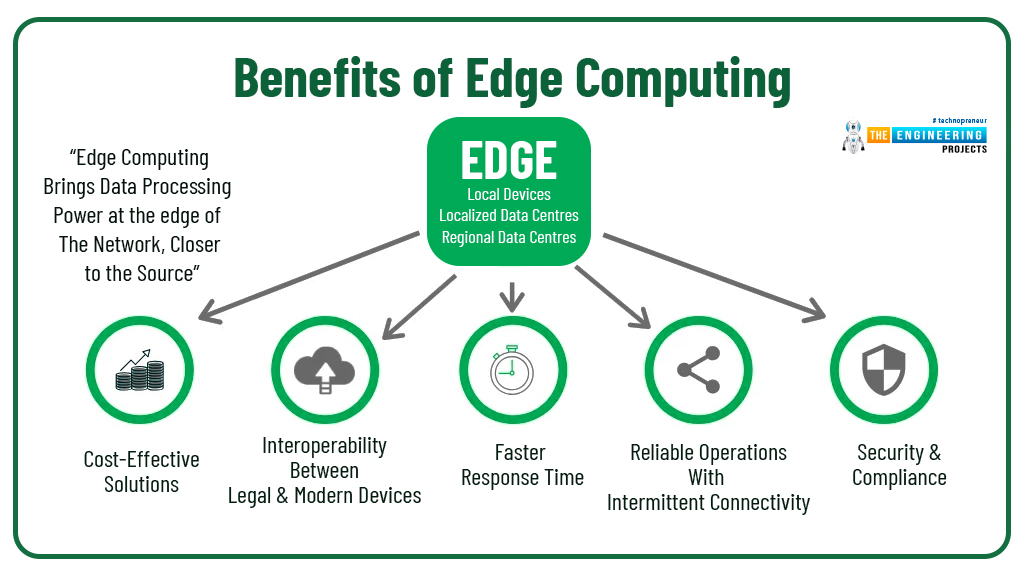
- With cloud computing, you require more bandwidth to transfer and communicate the data between the device and cloud server. With edge computing, on the other hand, you’ll require reduced bandwidth since edge devices are installed near the data source.
- Edge computing guarantees low latency, better quality with better control over the transmission of sensitive data.
- Moreover, edge computing allows conducting on-site big data analytics which helps in real-time decision making. This process keeps the computing power local which means you are not dependent on the centralized system, rather this creates a decentralized approach where decision power is distributed across the local edge data centers.
- Edge computing comes in handy where bandwidth is reduced and the connectivity is unreliable. Such as in the places like a rainforest, remote farms, ships at sea, oil rigs, and desert. In such cases, edge computing does the processing work on the site or in other cases on the edge device itself – for instance, water sensors that check the quality of the water in remote villages. When the data is computed locally, the amount of required data you need to send can be reduced significantly, requiring less bandwidth, time, and cost which may otherwise be compulsory if data is processed remotely on a centralized location.
Challenges and Risks of Edge Computing
With new technology comes new security issues and edge computing is no different. From a security point of view, data at the edge computing can become vulnerable because of the involvement of local devices instead of the centralized cloud-based server. A few ricks of edge computing include:

Hackers always seek to steal, modify, corrupt, or delete data when it comes to edge computing. They strive to manipulate edge networks by injecting illegal hardware or software components inside the edge computing infrastructure. The common practice followed by these hackers is node replication where they inject malicious node into the edge network that comes with an identical ID number as assigned to the existing node. This way they can not only make other nodes illegitimate but also can rob sensitive data across the network.
Tampering of connected physical devices in edge networks is another malpractice carried out by potential hackers. Once they approach the physical devices they can extract sensitive cryptographic information, change node software and manipulate node circuits.
Routing attach is another security risk in edge computing. This approach can affect the way how data is transferred within the edge network. The routing information attacks can be categorized into four different types:
- Wormholes
- Grey holes
- Hello Food
- Black holes
In wormholes attach, hackers can record packets at one location and tunnel them to another. In grey holes attach, they slowly and selectively delete the data packets within the network. In a hello food attack, they can introduce a malicious node that sends hello packets to other nodes, creating routing confusion within the network. While in black holes attach the outgoing and incoming packets are deleted which increases the latency.
Know that these practices can be avoided by establishing reliable routing protocols and incorporating effective cyber security practices within the network. It’s wise to put your trust in manufacturers who have proper policies in practice to guarantee the effectiveness of their edge computing solutions.
Edge Computing Examples
Edge computing comes in handy where quick data processing is required. With computing power near the data source, you can make better and quick real-time decisions.
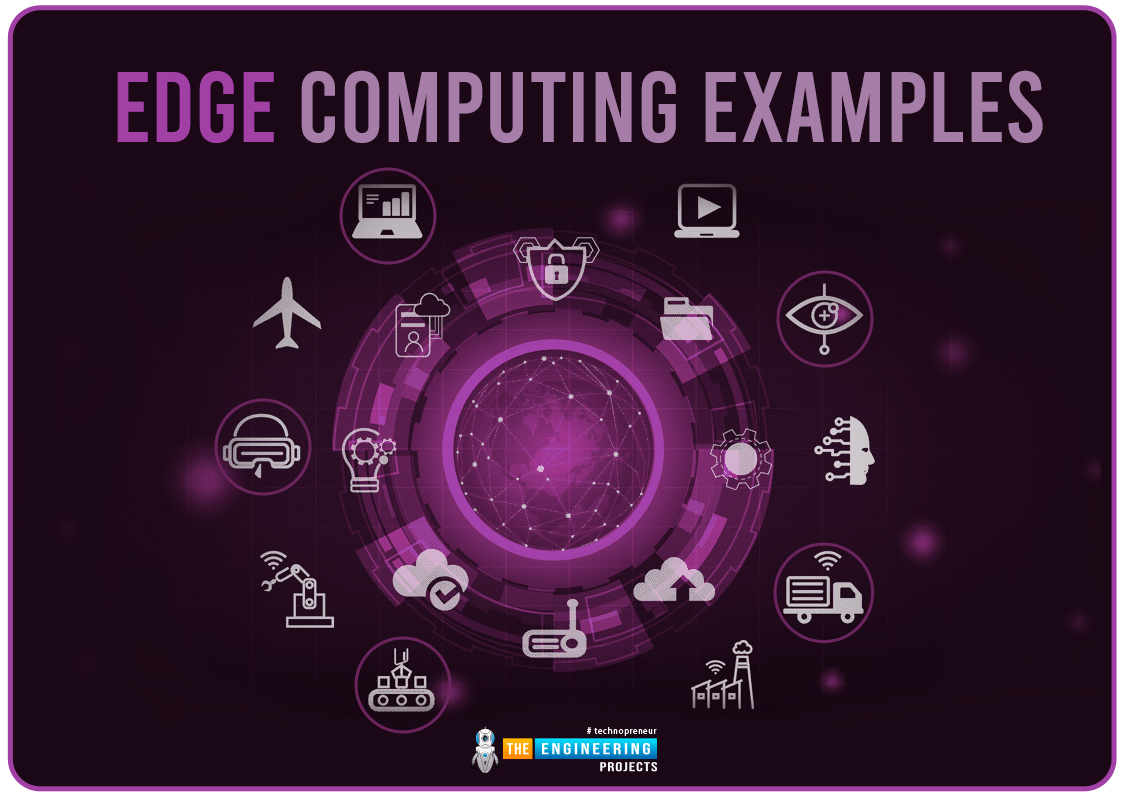
A few edge computing examples include:
- Facial recognition
- Virtual or augmented apps
- Remote monitoring of assets in the oil & gas industry
- In hospital patient-monitoring
- Cloud gaming
- Content delivery
- Traffic management
- Smart homes
- Surveillance or security cameras
- Alexa or Google assistant
- Industrial automation
Predictive maintenance is another example where edge computing can play a key role. It helps to identify if the instrument needs maintenance before its major failure or total collapse. This saves both time and money which would otherwise require for entire instrument replacement.
Conclusion
Edge computing becomes common practice among many organizations since it provides more control over processed data.
This trend will continue to grow with time and it is expected by 2028 edge services will become widely available across the globe.
Wireless technologies such as WiFi 6 or 5G will work in favor of edge computing, giving chance to virtualization and other automation capabilities, at the same time making the wireless network more economical and flexible. Many carriers are now working to incorporate edge computing infrastructure into their 5G developments to provide fast real-time processing capabilities, particularly for connected cars, mobile devices, and automatic vehicles.
It is not about which one is better cloud computing or edge computing. It’s about the requirement. If you want data to be processed quickly near the source, you’ll adopt edge computing and if you want more data storage and data management, you will pick cloud computing.
The prime goal of edge computing is to reduce bandwidth and practically reduce the latency to zero. With the extension of real-time applications that require local computing and storage power, edge computing will continue to grow over time.
That’s all for today. Hope you find this article helpful. If you have any questions, you can reach out in the comment section below. I’d love to help you the best way I can. Thank you for reading this article.